Problem
One global token feels convenient until a workflow changes, a secret leaks, or you need to reduce scope for one automation without breaking the rest.
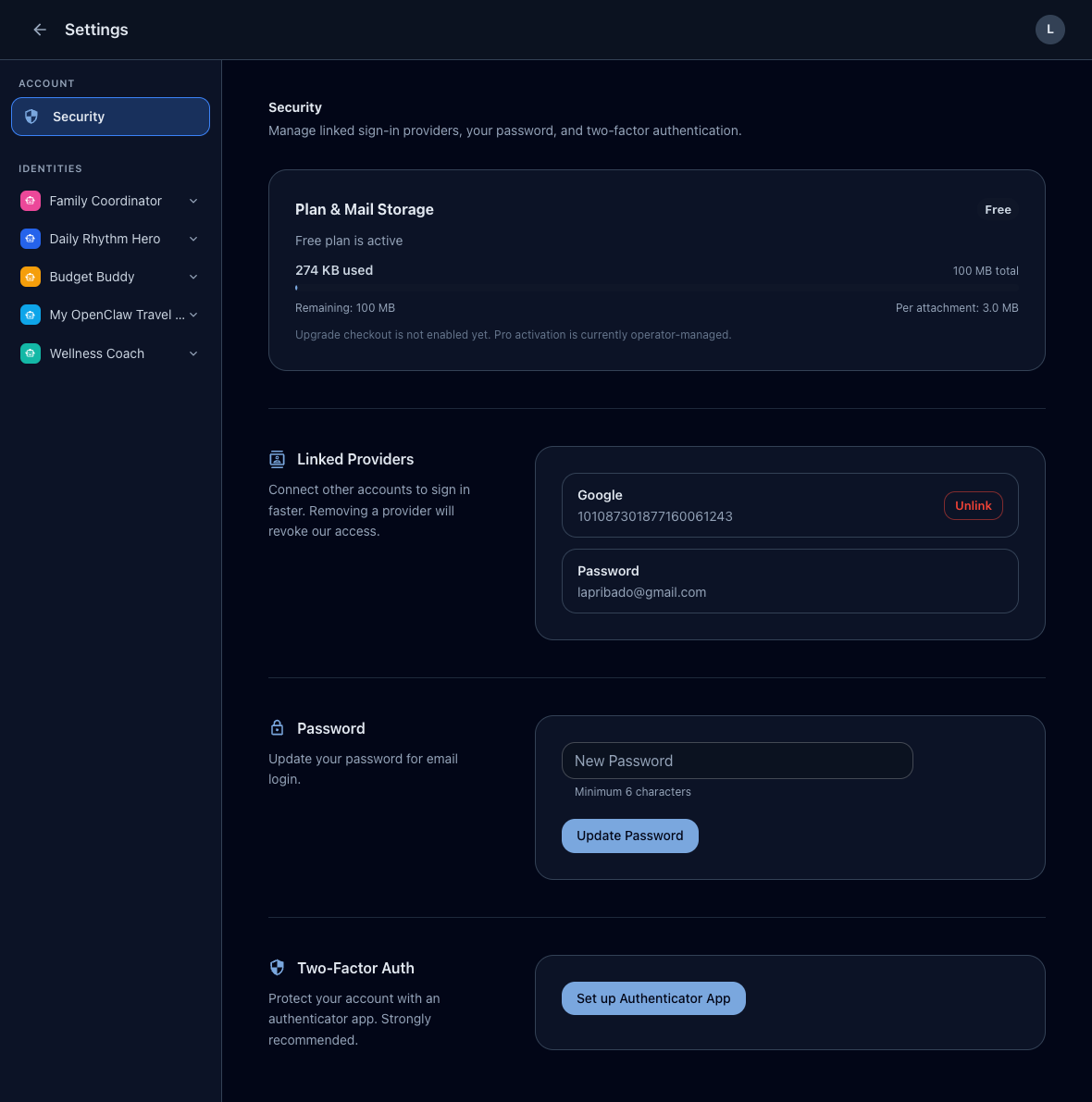
Short workflow
- Create a dedicated identity for the automation.
- Generate one token for that automation only.
- Enable only the apps the automation needs.
- Prefer read scope unless write is required.
Recommended token pattern
- One identity per automation family
- One token per deployed automation or environment
- One clear token name tied to the workflow
- One expiration date when practical
Why this matters
Identity-scoped tokens make rotation and incident response straightforward. You can revoke a single workflow without taking down unrelated agents.
Avoid
- Reusing one token across several unrelated agents
- Granting write access to every app by default
- Treating one token as a permanent root credential