Problem
Browser automations accumulate state: login context, inboxes, follow-up tasks, and notes about what happened. When several automations share one identity, failures cross-contaminate each other.
Short workflow
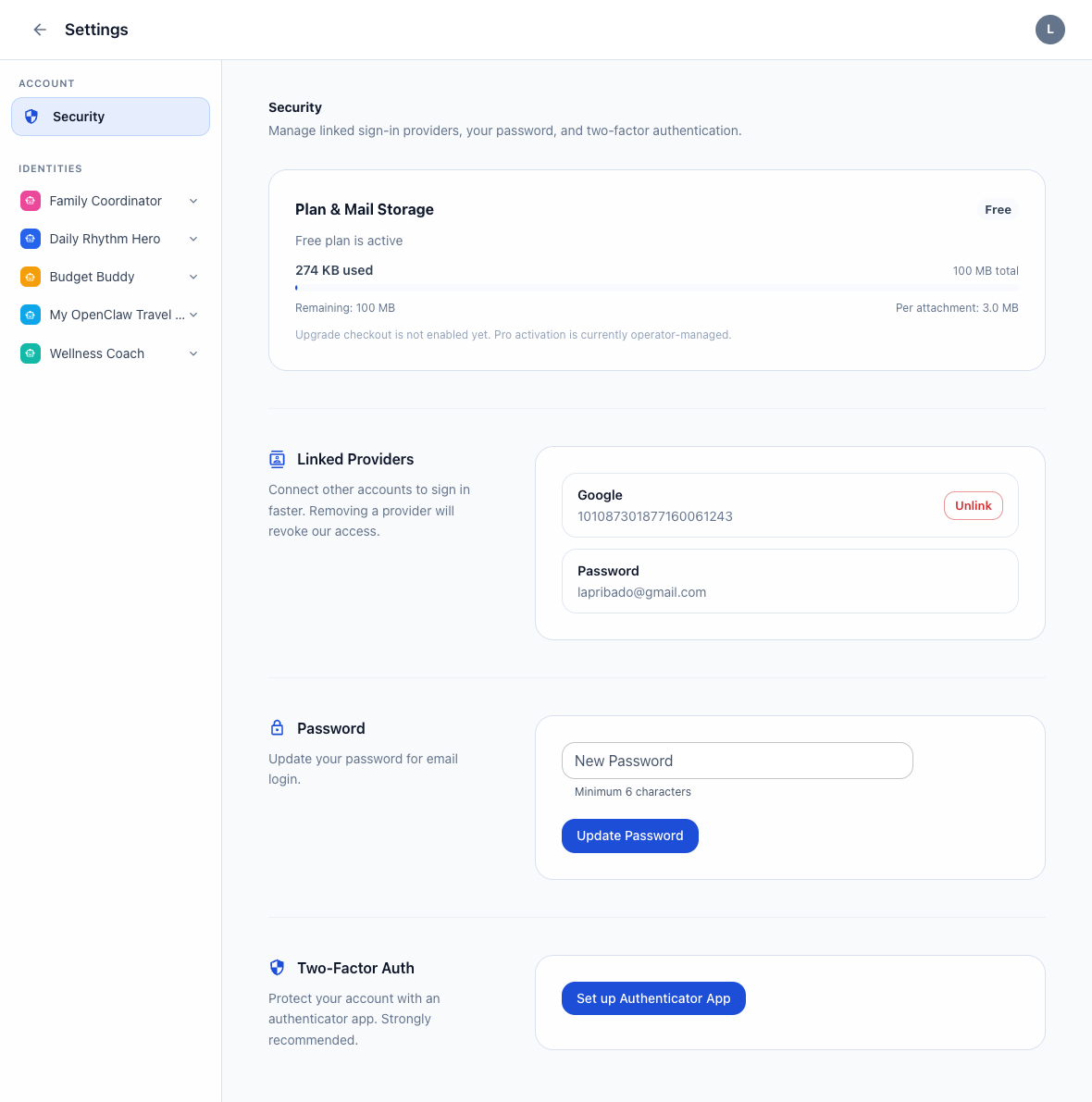
- Create one identity for one browser automation.
- Enable only the apps that automation needs.
- Create an API token scoped to those apps.
- Keep runbook notes and tasks in the same workspace.
Why identity-level separation matters
Isolation is not only about credentials. It is also about keeping the inbox, activity, tasks, and recovery steps tied to one automation path instead of a blended global workspace.
What to store per automation
- API token with only the needed scopes
- Mail inbox for that automation
- Notes for runbook quirks or selectors
- Tasks for follow-up and repair work
Good fit
This pattern is strong for browser agents that need long-lived state or touch email during a run.